Phishing Website Evolution: Perfect High-Fidelity Login Pages Generated by Large Models – Essential Anti-Fraud Course for BiyaPay Users
Image Source: unsplash
Have you noticed that phishing website evolution has entered a completely new stage? Today, many attackers use large model technology to generate almost indistinguishable high-fidelity login pages. When you operate your BiyaPay account in daily use, a moment of carelessness could lead you into a trap. According to CybelAngel’s 2025 External Threat Intelligence Report, up to 67.4% of phishing attacks involve AI-generated content. The table below shows the proportion of AI-generated content in phishing attacks reported by multiple sources:
| Source | Percentage of Phishing Attacks Involving AI-Generated Content |
|---|---|
| CybelAngel 2025 External Threat Intelligence Report | 67.4% |
| Hoxhunt Phishing Trends Report 2025 | <5% (phishing that bypasses email filters) |
| Mimecast 2025 Research | 12% (phishing caught by email filters) |
Only by possessing the ability to recognize and defend can you protect the security of your account assets. Staying vigilant and actively improving anti-fraud awareness is an essential course for every Chinese-speaking user.
Key Takeaways
- Stay vigilant and regularly check the security settings of your BiyaPay account to ensure multi-factor authentication is enabled and enhance account protection.
- Carefully verify the domain name and security certificate of the login page to ensure they match official information and avoid falling into phishing traps.
- Recognize common forgery techniques in phishing emails, be wary of urgency and unnatural expressions, and avoid blindly trusting suspicious requests.
- Use email security tools and browser extensions to automatically detect phishing websites and strengthen protection.
- When encountering suspicious pages, immediately stop operations and verify through official channels to protect personal information security.
Phishing Website Evolution and Large Model Applications

Image Source: unsplash
Large Models Empower Phishing Website Upgrades
You will find that the speed of phishing website evolution far exceeds previous levels. Large Language Models (LLMs) enable attackers to automate various stages of phishing attacks, including reconnaissance, email generation, and attack effectiveness tracking. Now, AI-automated information scraping tools can discover accurate and useful information in 88% of cases, greatly improving attack efficiency. You can refer to the table below to understand the key roles of AI large models in phishing website evolution:
| Evidence Type | Details |
|---|---|
| AI Automated Phishing Capability | In 88% of cases, AI tools can discover accurate and useful information |
| Phishing Email Effectiveness | AI-generated phishing emails reach the level of human experts |
| Research Progress | AI-enhanced phishing attacks are becoming increasingly sophisticated and difficult to defend against |
You also need to note that AI-powered website builders allow attackers to generate high-fidelity phishing sites in seconds, significantly lowering the technical barrier.
Principles of High-Fidelity Login Pages
The generation of high-fidelity login pages mainly relies on cloning technology and psychological manipulation. Attackers use phishing toolkits to directly copy the HTML code of legitimate websites, producing almost identical interfaces. This makes it very difficult for you to distinguish real from fake based on appearance alone. At the same time, attackers exploit psychological factors such as fear and urgency to induce you to quickly enter account information. Compared with traditional phishing websites, AI-generated pages have no spelling or grammatical errors, feature more professional content, and are highly deceptive.
| Evidence Type | Description |
|---|---|
| AI-Generated Phishing Websites | Attackers can generate phishing sites in seconds using AI-driven tools |
| Traditional Phishing Attacks | Common spelling and grammar errors, chaotic formatting, easy to identify |
| AI Advantages | Grammatically correct, voice cloning, context awareness — phishing attempts much harder to detect |
Characteristics of New Phishing Pages
When identifying new pages resulting from phishing website evolution, you should pay attention to the following characteristics:
- Modern phishing pages often use reverse proxy technology to steal sessions in real time and bypass multi-factor authentication (MFA).
- Attackers utilize multi-stage redirect chains to hide malicious pages among multiple legitimate pages, increasing detection difficulty.
- Pages may integrate custom captchas or Cloudflare Turnstile to prevent security tools from analyzing them.
- Phishing pages adopt multi-stage loading, displaying malicious content only under specific conditions to reduce the probability of detection.
These new characteristics make high-fidelity login pages after phishing website evolution more concealed and dangerous. You need to continuously improve security awareness to effectively defend against them.
Phishing Attack Cases Targeting BiyaPay
Common Forgery Techniques
When you use BiyaPay daily, you often encounter various phishing attack techniques. Attackers continuously leverage new technologies brought by phishing website evolution to enhance the concealment and deceptiveness of forgeries. You need to focus on the following common forgery methods:
- Identify fake payment requests. Attackers often impersonate platforms or partners you trust and send emails requesting payments or information.
- Create a sense of urgency. You receive messages claiming “failure to act immediately will result in account freezing or fund loss,” inducing quick reactions.
- Check information consistency. You should verify whether the sender’s email matches the official domain and be wary of links pointing to unfamiliar websites.
- Identify grammar and spelling errors. Although errors have decreased after phishing website evolution, you still need to watch for unnatural expressions.
- Be cautious with suspicious attachments. When receiving attachments from unknown sources, avoid opening them directly.
- Beware of abnormal requests. Attackers may ask you to click links to install programs or enter sensitive information.
- Verify requesters of sensitive information. When receiving requests from suppliers to change bank accounts or other sensitive information, you must verify through independent channels.
Case Analysis
You can understand the specific threats that phishing website evolution poses to BiyaPay users through the following case. Recently, Chinese-speaking users received an email that appeared to come from BiyaPay, stating “Abnormal login detected on your account, please verify your identity immediately.” The email page was highly realistic, with the domain differing by only one character. After clicking, the user entered a high-fidelity login page, and after inputting account details and verification code, the attacker stole session information in real time, bypassing multi-factor authentication. Due to the use of multi-stage redirects and reverse proxy technology, security tools had difficulty detecting the anomaly in time. If you do not carefully verify the domain and security certificate, you can easily leak account information in such attacks.
You should always remain vigilant, combining visual details and technical means to improve your ability to recognize new attacks brought by phishing website evolution.
Identifying High-Fidelity Login Pages After Phishing Website Evolution
Visual and Interaction Detail Differentiation
When facing high-fidelity login pages after phishing website evolution, visual and interaction details serve as your first line of defense. Page designs are becoming increasingly realistic, but you can still discover anomalies through careful observation. You can focus on the following aspects:
-
Domain and Certificate Verification
You should carefully check the domain of the login page. High-fidelity pages often use domains that differ from the official one by only one character or employ similar spellings. Click the browser address bar to check for HTTPS encryption and verify whether the security certificate is issued by a trusted authority. Mismatched certificate information or abnormal domain spelling are typical signs of phishing website evolution. -
Page Details and Layout
You can observe fonts, colors, and button styles. Although high-fidelity pages appear consistent overall, details often have flaws. For example, inconsistent button response speed, slight font differences, blurry images, or slow loading. You can also try switching languages or themes — some phishing pages fail to switch properly or display incomplete content. -
Interaction Flow and Prompt Messages
When entering account information, if the page shows abnormal prompts or the flow differs from the official one, stay alert. High-fidelity pages may lack official security prompts, verification mechanisms, or multi-factor authentication processes. You can try entering incorrect information and observe the page’s response. Official pages usually provide detailed error messages, while phishing pages may redirect immediately or provide no feedback.
Tip:
When encountering any suspicious page, it is recommended to pause operations and first verify through official channels. Do not trust urgent prompts or countdown warnings on the page — these are common tactics used after phishing website evolution to induce users.
Technical Assistance Identification Methods
You can use various technical tools to improve your ability to recognize high-fidelity login pages. Technical means not only compensate for limitations of visual identification but also provide active defense against new phishing attacks.
-
Email Security and Anti-Phishing Tools
You can use email security gateways, email filters, antivirus software, and anti-malware tools. These tools can automatically detect and block most phishing attempts. You can also install browser security extensions to monitor webpage content in real time and identify malicious links and forged pages. -
Layered Security Strategy
You can adopt a layered security strategy, covering protection measures across email, browser, operating system, and other layers. This ensures that even if one layer is breached, other layers still provide protection. -
Keyword and Content Analysis
You can focus on specific keywords in page content. Recent research shows that phishing pages often contain words like “urgent,” “verify,” and “account abnormal.” You can use webpage content analysis tools to automatically detect these keywords and improve recognition efficiency. -
Machine Learning Algorithm-Assisted Detection
Some security vendors and researchers have applied machine learning algorithms to phishing detection. You can choose security tools that support AI detection — these tools can automatically determine high-fidelity phishing pages after evolution based on page structure and content features, with significantly improved accuracy.
| Tool Type | Function Description |
|---|---|
| Email Security Gateway | Automatically intercepts phishing emails, filters malicious attachments and links |
| Browser Security Extension | Real-time webpage monitoring, identifies forged pages and malicious scripts |
| Antivirus & Anti-Malware | Detects and removes phishing-related malicious programs |
| Content Analysis Tool | Checks page keywords to assist in identifying phishing characteristics |
| AI Detection Tool | Uses machine learning algorithms to automatically identify high-fidelity phishing pages |
In actual operations, you can combine visual details with technical tools to form a multi-layered protection system. Although phishing website evolution continuously improves forgery capabilities, as long as you stay vigilant and make good use of tools, you can effectively identify and defend against risks brought by high-fidelity login pages.
Essential Anti-Fraud Course for BiyaPay Users

Image Source: unsplash
Anti-Fraud Techniques
When operating your BiyaPay account daily, you must master a set of practical anti-fraud techniques. Phishing website evolution makes attacker methods more concealed — only active protection can safeguard your asset security. The following are expert-recommended anti-fraud measures:
- Stay vigilant and recognize phishing or impersonation tactics used by cybercriminals.
- Change passwords regularly to ensure account authentication security.
- Verify every transaction to ensure recipient information is accurate.
- Avoid operating in insecure network environments.
- Enable transaction notification to promptly detect abnormal activity.
- Enable multi-factor authentication to add an extra security layer to your account.
- Use strong encryption technology to protect data.
- Conduct regular security audits to identify potential vulnerabilities.
- Carefully verify the recipient and amount before each operation to avoid losses due to errors.
You can apply these techniques to global payments and receipts, international remittances, fiat and digital currency exchanges, and other scenarios. For example, when receiving funds through a licensed Hong Kong bank, you should verify recipient information to ensure the USD amount is correct. You can also enable BiyaPay’s multi-factor authentication and transaction notification features to detect abnormal operations immediately.
Official Security Recommendations
When defending against risks brought by phishing website evolution, you must follow official security recommendations. Multi-factor authentication (MFA) has become the most effective measure to prevent credential theft and phishing. Experts point out that hackers often gain access through login rather than directly invading systems. After enabling MFA, even if attackers obtain your password, it is difficult for them to breach your account defenses.
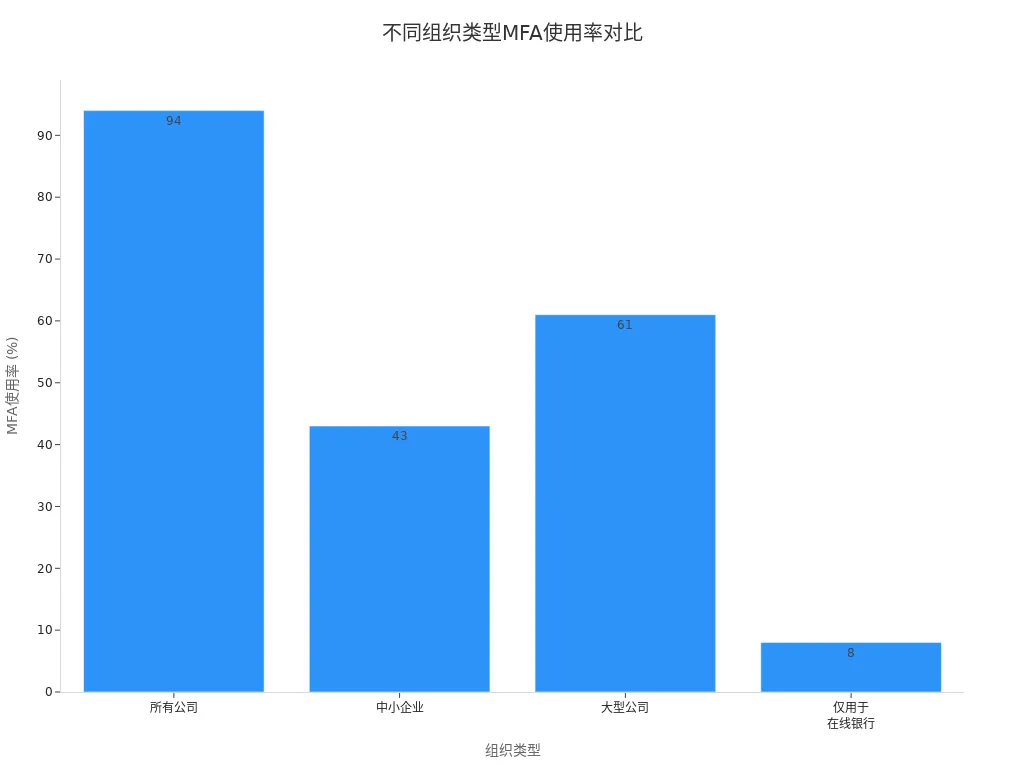
The table below shows the adoption rate of MFA across different organization types:
| Organization Type | MFA Adoption Rate |
|---|---|
| All Companies | 94% |
| Small and Medium Enterprises | 43% |
| Large Companies | 61% |
| Online Banking Only | 8% |
You can refer to the bar chart below to intuitively understand MFA usage across different organization types:
You should also use a password manager and change passwords regularly to avoid reuse. BiyaPay supports strong encryption technology and multi-layer security protection — you can combine official tools to elevate your account security level. When performing deposits and withdrawals for US stocks or Hong Kong stocks, always verify the platform’s security certificate to ensure a reliable trading environment.
Besides checking certificates and domains, consistently entering key pages through the same official route can also reduce the chance of landing on a high-fidelity fake login page. For users who need to review market data, access trading accounts, or continue with follow-up actions, a safer practice is to go directly through the BiyaPay website or the official stock information page, instead of using search ads, unfamiliar chat links, or third-party redirect pages.
If asset-related actions are required afterward, it is also better to continue through the unified trading entry. As a multi-asset trading wallet, BiyaPay keeps account access, trading, and fund management within one system, which helps reduce risks caused by spoofed pages, altered links, and unnecessary redirects. In security-sensitive scenarios like this, keeping the access path fixed and verifiable is more reliable than making a last-minute judgment about whether a page looks real.
Tip:
When encountering any suspicious operation, immediately pause the transaction and verify information through BiyaPay official channels. Do not trust urgent prompts in unfamiliar emails or text messages to avoid asset losses caused by phishing website evolution.
Phishing Website Response Process
When you discover a suspected phishing website, you should quickly follow this response process:
-
Immediately Stop Operations
When you find page anomalies or receive suspicious information, stop entering any account or transaction information immediately. -
Verify Domain and Certificate
Check whether the page domain matches BiyaPay’s official domain and verify that the security certificate is issued by a trusted authority. -
Contact Official Customer Service
Report suspicious pages or transactions through BiyaPay official channels or in-app customer service and seek professional assistance. -
Change Account Password
If you suspect information leakage, immediately change your account password and enable multi-factor authentication to prevent further risks. -
Monitor Account Activity
Enable transaction notifications to monitor account fund flows in real time and handle any anomalies promptly. -
Submit Security Report
When encountering new attacks after phishing website evolution, submit a security report to BiyaPay official channels to help the platform improve protection measures.
In global payments and receipts, digital currency exchange, international remittance, and other business scenarios, always stay vigilant and strictly follow the response process. Only by forming good security habits can you effectively defend against new risks brought by phishing website evolution.
Facing phishing website evolution driven by large models, you must continuously improve anti-fraud awareness. You can reduce risks by regularly learning to recognize phishing techniques, verifying the identity of requesters of sensitive information, checking sender addresses, avoiding clicking suspicious links, and enabling two-factor authentication. By developing good security habits and actively using BiyaPay official tools, you can effectively protect account security. Together with other Chinese-speaking users, your efforts will contribute to a higher level of security in the global online environment.
FAQ
How to quickly determine if a login page is a phishing website?
You can first check the domain spelling and security certificate. You can also try switching the page language or theme to observe whether the content is complete. When page details are abnormal, it is recommended to pause operations and verify through official channels.
What should you do if you accidentally enter account information?
You should immediately change your account password and enable multi-factor authentication. You also need to contact BiyaPay official customer service, report the risk, and monitor account fund flows to prevent further losses.
How does BiyaPay ensure security for global payments and receipts?
BiyaPay adopts multi-layer encryption technology and multi-factor authentication. You can enable transaction notifications to stay informed of account dynamics in real time. The platform also supports regular security audits to help you identify potential risks promptly.
Why is it recommended to use licensed Hong Kong banks for receiving payments?
Choosing licensed Hong Kong banks for receiving payments provides higher compliance assurance and fund security. You can also enjoy more convenient USD settlement services, reducing cross-border operation risks.
How does multi-factor authentication help account security?
After enabling multi-factor authentication, even if attackers obtain your password, they will find it difficult to log in to your account. You can significantly improve your account security level and prevent asset theft by phishing websites.
*This article is provided for general information purposes and does not constitute legal, tax or other professional advice from BiyaPay or its subsidiaries and its affiliates, and it is not intended as a substitute for obtaining advice from a financial advisor or any other professional.
We make no representations, warranties or warranties, express or implied, as to the accuracy, completeness or timeliness of the contents of this publication.
Related Blogs of

How Do Zero-Commission U.S. Stock Trading Platforms Make Money? Fees and Service Models Explained

Remitly Transfer Fees and Limits: How Much You Can Send and What It Costs
Choose Country or Region to Read Local Blog
Contact Us
BIYA GLOBAL LLC is registered with the Financial Crimes Enforcement Network (FinCEN), an agency under the U.S. Department of the Treasury, as a Money Services Business (MSB), with registration number 31000218637349, and regulated by the Financial Crimes Enforcement Network (FinCEN).
BIYA GLOBAL LIMITED is a registered Financial Service Provider (FSP) in New Zealand, with registration number FSP1007221, and is also a registered member of the Financial Services Complaints Limited (FSCL), an independent dispute resolution scheme in New Zealand.



















