Why 'Never Trust Any Code'? Returning to Cold Wallets and Hardware Authentication in the Age of Automation

Image Source: unsplash
In the blockchain world, you often hear the advice: never trust any code. Even smart contracts that have undergone professional audits have led to numerous projects being exploited due to vulnerabilities or design flaws. The table below shows the common attack types and their proportions:
| Attack Type | Percentage |
|---|---|
| Reentrancy attacks | 26% |
| Flash loan attacks | 11% |
| Unaudited projects | 90% |
With the widespread adoption of automation and smart contracts, asset security risks continue to rise. You may encounter the following threats:
- SIM card swapping
- Wallet drainers
- Exchange vulnerabilities
- Social engineering manipulation of smart contracts
To control risks, you can choose tools such as cold wallets and hardware authentication to proactively improve the security level of your digital assets.
Key Takeaways
- Code vulnerabilities can lead to massive losses; historical cases show that even audited projects are not safe.
- Cold wallets store private keys offline, effectively isolating them from network attacks—ideal for long-term storage of digital assets.
- Hardware wallets provide physical isolation to prevent malware attacks and ensure transaction security.
- Multi-factor authentication enhances security—even if passwords are stolen, attackers cannot easily access assets.
- Regularly review dependencies and security settings, stay vigilant, and guard against social engineering and phishing attacks.
Risks of “Never Trust Any Code”
Image Source: unsplash
Code Vulnerability Case Studies
In the blockchain space, you frequently hear “never trust any code” because many major historical security incidents originated from code vulnerabilities. Even when development teams invest significant effort in testing and auditing, risks cannot be completely eliminated. The table below presents several well-known blockchain projects that suffered massive losses due to code vulnerabilities:
| Incident | Loss Amount | Vulnerability Type |
|---|---|---|
| Wormhole bridge attack | $324,000,000 | Lack of input validation |
| The DAO attack | $150,000,000 | Recursive call vulnerability |
| Parity multi-sig wallet | $30,000,000 | Access control vulnerability |
| Mango Markets attack | $112,000,000 | Price oracle manipulation |
| MonoX logic error | $31,000,000 | Logic error |
You can see that a single vulnerability can cause losses ranging from tens of millions to hundreds of millions of dollars. The chart below visually illustrates the economic impact of these incidents:
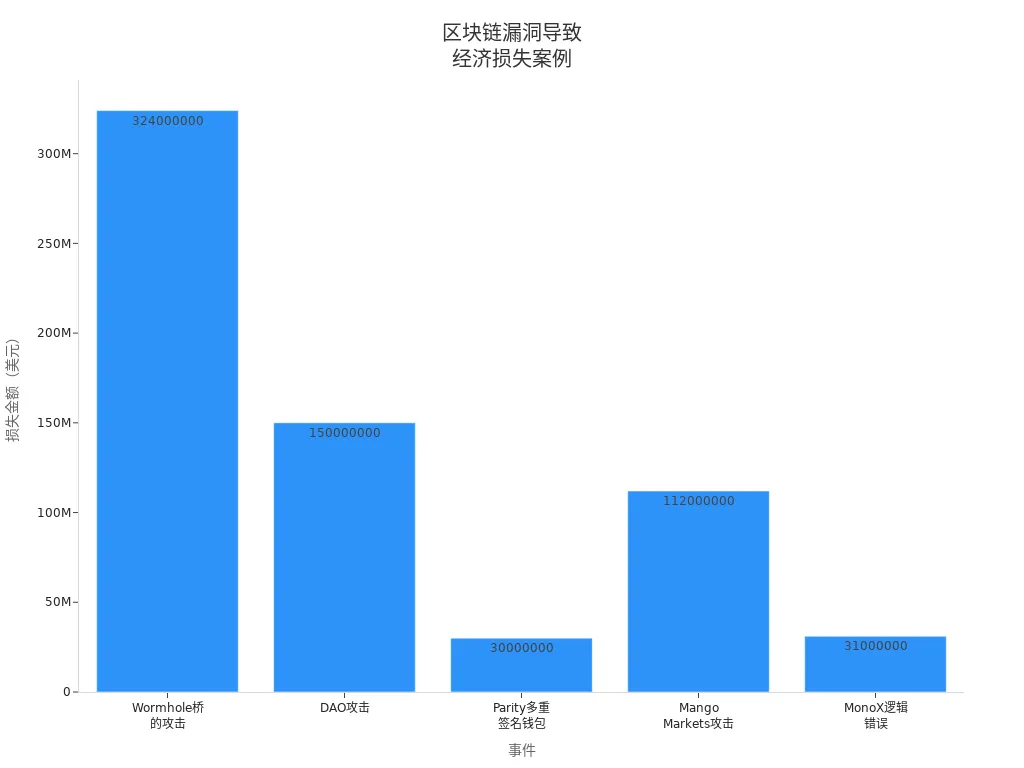
These events remind you that code itself should not be fully trusted. Even projects that undergo multiple rounds of auditing may still contain hidden backdoors or logic flaws. “Never trust any code” has become a fundamental principle in the field of digital asset security.
Smart Contract Automation Risks
The automation feature of smart contracts allows complex operations to be completed without human intervention, but it also introduces new attack surfaces. Automation enables attackers to search for and exploit vulnerabilities in bulk and at high speed. You need to be vigilant about the following common risks:
- Front-running attacks: Attackers use information from unconfirmed transactions and increase miner fees to prioritize their own transactions, gaining unfair advantages.
- Denial-of-Service (DoS) attacks: Attackers create transactions that consume large amounts of resources, causing smart contracts to malfunction and resulting in financial losses.
- Logic errors: Smart contract code behaves differently from expected, leading to function disruption or fund losses.
- Insecure randomness: Attackers exploit blockchain pseudo-random number generation mechanisms to affect fairness in gaming or lottery contracts.
Automation makes attacks more efficient and covert. You cannot rely on traditional manual review to detect all risks in time. “Never trust any code” becomes especially important in the automated environment of smart contracts.
Limitations of Code Auditing
You may believe that code auditing can eliminate most risks, but the reality is far more complex. Auditing tools and processes have clear limitations:
| Evidence Type | Specific Content |
|---|---|
| Limitations of automated tools | Current security tools can only detect 8–20% of exploitable vulnerabilities; automated vulnerability discovery is severely insufficient. |
| Importance of human factors | Human involvement is critical for discovering uncommon vulnerabilities, logic errors, and economic factors—automated tools cannot replace it. |
| Comprehensive security strategy | Automated tools are good at finding common coding errors, but full security requires combining manual review and contextual analysis. |
You need to understand that auditing is not omnipotent. Automated tools cover only a limited scope, and manual review may miss critical issues due to lack of experience or time pressure. “Never trust any code” is not only a warning to developers but also a principle you must keep in mind when managing assets.
Throughout digital asset management, you should always remain vigilant. Code vulnerabilities, automation risks, and auditing limitations together create complex security challenges. Only by adhering to “never trust any code” can you minimize the possibility of asset losses.
Expanding Attack Surface and New Threats
Automated Attack Tools
You will notice that as the automation level of digital asset platforms increases, the attack surface is also continuously expanding. Attackers use automated tools for asset discovery, vulnerability scanning, and rapid response, greatly improving attack efficiency. Today, Attack Surface Management (ASM) tools not only monitor on-premises assets but also provide full coverage of cloud resources. Machine learning and artificial intelligence technologies drive ASM development, bringing predictive analytics and anomaly detection capabilities. Automated incident response mechanisms make cyber threat handling faster. Manual processes can no longer cope with the scale of modern infrastructure—automation has become the mainstream trend. You need to pay attention to the following new changes:
- ASM tools achieve full visibility of assets, covering both cloud and on-premises environments.
- Automated vulnerability checks and response speeds far exceed manual capabilities.
- AI and ML technologies improve anomaly detection and prediction capabilities.
- Automated incident response mechanisms address complex threats.
Supply Chain and Dependency Risks
When using digital asset platforms, you often rely on third-party libraries, plugins, and services. Supply chain attacks have become an emerging threat—attackers tamper with dependency components or inject malicious code, indirectly compromising your asset security. You cannot fully control all dependencies, and risks increase accordingly. The table below shows common supply chain risks:
| Risk Type | Impact Method |
|---|---|
| Third-party library vulnerabilities | Asset leakage, theft |
| Malicious code in plugins | Backdoors, data tampering |
| Hijacked API interfaces | Transactions intercepted or altered |
You need to regularly review dependencies and monitor official security announcements to reduce unnecessary third-party integrations.
Social Engineering and Phishing
Attackers not only rely on technical means but also use social engineering and phishing strategies to trick you into disclosing sensitive information. You may encounter the following common tactics:
- Fake exchange websites: Attackers imitate well-known platforms to steal your login credentials and quickly drain accounts.
- Wallet phishing attacks: Fake wallet apps or websites induce you to enter recovery phrases and steal assets.
- Social media impersonation: Attackers impersonate celebrities or project founders on social platforms to conduct phishing campaigns.
You need to stay vigilant, verify the source of websites and applications, and avoid entering sensitive information on untrusted channels. Social engineering attacks often exploit your trust and carelessness—awareness is the most effective protective measure.
Security Advantages of Cold Wallets

Image Source: unsplash
Cold Wallets Isolate Network Risks
When managing digital assets, cold wallets store private keys offline, effectively isolating them from network risks. Cold wallets do not connect to the internet, resulting in a minimal attack surface and making it extremely difficult for hackers to remotely access your assets. The table below compares cold wallets and hot wallets in terms of risk level and security characteristics:
| Wallet Type | Connection Status | Risk Level |
|---|---|---|
| Cold wallet | Offline | Low |
| Hot wallet | Online | High |
| Wallet Type | Security Feature | Attack Surface |
|---|---|---|
| Cold wallet | No internet connection | Minimal |
| Hot wallet | Connected to the internet | Large |
Cold wallets use offline signing mechanisms, ensuring private keys are never exposed to any networked device. You can transmit signed data securely via encrypted QR codes. Some cold wallets also use CC EAL6+ chips to protect private keys against physical attacks and reverse engineering. Throughout asset management, you must always remember “never trust any code”—the physical isolation of cold wallets provides the most direct protection.
Cold Wallet Use Cases
If you plan to hold large amounts of cryptocurrency long-term, cold wallets are the best choice. Cold wallets are completely offline, isolating private keys from the internet—ideal for long-term storage and protection against platform failures or hacker attacks. The table below summarizes recommended use cases for cold wallets:
| Evidence Type | Description |
|---|---|
| Long-term storage | Cold wallets provide enhanced security suitable for long-term holding of large amounts of cryptocurrency. |
| Protective measure | Cold wallets store cryptocurrency offline to prevent network attacks. |
- Suitable for long-term storage of large amounts of cryptocurrency
- Protects against online hacker attacks
- Ideal for users who want to keep the majority of assets in cold storage
In scenarios such as global payments, cryptocurrency trading, and asset exchange, you can choose services like BiyaPay that support cold wallet management to ensure fund security. Cold wallets have become the gold standard for long-term digital asset storage, especially suitable for Chinese-speaking users during cross-border remittances and asset allocation.
Cold Wallet Precautions
When using cold wallets, you need to pay attention to the following security details:
- Ensure the device has a backup in case of loss.
- Store backups securely to prevent others from accessing funds.
- Create the wallet in a completely private environment, avoiding cameras and screen sharing.
- Manually record the recovery phrase—never take photos or store it digitally.
- Verify the recovery phrase to ensure the backup is correct.
- Set a PIN or enable biometrics to enhance physical security.
- Install the official companion app, such as BiyaPay or other services that support cold wallet management, for convenient subsequent operations.
- Perform small-amount transfer tests to confirm the device and process are secure and reliable.
By following these precautions, you can effectively prevent common supply chain and initialization security risks.
Hardware Authentication Protection Role
When managing digital assets, hardware wallets provide physical isolation for private keys. The device stores private keys completely offline, avoiding attacks from computer viruses and hackers. You have physical control over the device, and all transactions require authorization through the device. Hardware wallets have built-in screens that allow you to confirm transaction details before signing. Even if your computer or phone is infected with malware, the device can still protect your asset security. You can securely access and manage assets from any computer without worrying about private key exposure. Hardware wallets typically use secure microcontrollers to generate and protect private keys. Unsigned data is sent from the computer to the device; after you confirm on the screen, the device internally completes the signing, and the private key is never exposed in a networked environment.
- By storing private keys offline, hardware wallets significantly reduce exposure risk, effectively defending against malware, phishing, and data breaches.
- Secure elements simplify system architecture, reduce potential attack entry points, and ensure sensitive data remains secure even when facing software vulnerability exploits.
- Secure elements can resist fault injection and side-channel attacks, detect anomalies, and perform dummy operations to protect data.
- The device runs dummy operations in parallel with real operations to resist side-channel attacks, making it difficult for attackers to interpret the private key.
When choosing a hardware wallet, you can consider products that support hardware authentication, such as BiyaPay, to enhance asset security.
Multi-Factor Authentication
In digital asset management, adopting multi-factor authentication can further improve security levels. Multi-factor authentication requires you to provide multiple forms of verification, such as password plus hardware device confirmation. Even if attackers obtain your password, they cannot easily access assets without the physical device. The table below shows the advantages of multi-factor authentication:
| Evidence Type | Description |
|---|---|
| Multi-factor authentication | Enhances security by requiring users to provide multiple verification forms |
| Attacker difficulty | Even if attackers obtain the password, unauthorized access remains difficult |
In daily operations, it is recommended to enable multiple protection measures such as PIN codes, physical confirmation, and recovery phrases simultaneously to minimize risks. Never trust any code—only multi-factor authentication combined with physical isolation can truly safeguard your assets.
Configuration and Management Recommendations
When configuring and managing hardware authentication devices, follow best practices to ensure the device is secure and reliable.
- Purchase directly from the manufacturer, avoid third-party sellers to prevent supply chain attacks.
- Verify device authenticity—check tamper-evident packaging and run the manufacturer’s verification tool.
- Regularly update firmware to patch known vulnerabilities in a timely manner.
- Test the recovery process and verify seed phrase backup validity before transferring large amounts of funds.
- Use the passphrase feature to add an extra security layer to the mnemonic seed.
Throughout asset management, always stay vigilant and regularly check device status and backup security. Only by strictly following security processes can you effectively defend against cyber attacks and malware in the age of automation and protect your digital assets.
Hot Wallet Security Recommendations
Choosing Officially Verified Wallets
When selecting a hot wallet, prioritize officially verified or mainstream open-source projects. Reputable wallets undergo multiple rounds of review by the community and security teams and can promptly fix known vulnerabilities. You should obtain the latest version from the wallet’s official website or authoritative open-source platforms and avoid downloading tampered or malware-injected applications. You also need to pay attention to the wallet’s update frequency and community activity—these factors directly affect wallet security and maintainability. Before installing a wallet, carefully verify developer information and digital signatures to ensure the source is trustworthy.
If you need both long-term storage and a smaller balance for routine transfers or reallocation, a safer approach is to separate assets by purpose. Keep long-term holdings in cold storage, and leave only operational funds in an active account under official channels, rather than exposing your entire balance to a high-frequency online environment.
Using the BiyaPay website as an example, payments, trading, and fund management can be handled within one multi-asset wallet system. When action is actually needed, it is still better to enter through the official trading entry instead of jumping through unknown plugins, scripts, or mirror pages; in practice, that is also an extension of the idea that you should never trust any code too easily.
Device Lock Screen and Security Settings
On devices used for hot wallets, you must enable lock screen passwords, fingerprint, or facial recognition security measures. This prevents unauthorized access to your wallet when you leave the device unattended. You should also enable full-disk encryption to protect data if the device is lost or stolen. Regularly update the operating system and wallet application and install security patches promptly to defend against emerging malware and attack methods. You can dedicate a phone or computer specifically for cryptocurrency operations to reduce mixing with daily entertainment and social applications, further lowering risk.
Daily Security Habits
Developing good security habits when managing hot wallets daily is crucial. The following recommendations can help you minimize asset risk to the greatest extent:
- Keep software and systems updated promptly to patch security vulnerabilities
- Regularly scan for malicious programs using antivirus software
- Enable full-disk encryption to prevent data leakage if the device is lost
- Avoid operating wallets on public Wi-Fi; use a VPN when necessary
- Configure a dedicated device for cryptocurrency to reduce cross-infection risk
- Use strong passwords and set independent passwords for each wallet
- Enable two-factor authentication, preferably using hardware keys
- Carefully double-check recipient addresses before sending to prevent address tampering
- Regularly revoke unnecessary dApp authorizations and limit wallet permissions
- Create offline secure backups of mnemonic phrases and store them in multiple safe locations
- Never disclose mnemonic phrases to anyone—be wary of phishing traps
- Carefully verify URLs before entering credentials to avoid fake websites
- Remain skeptical of any urgent-sounding requests
- Perform small test transfers before large transactions
- Continuously stay informed about the latest scam techniques and security updates
By consistently following these security habits, you can significantly reduce the probability of hot wallet attacks or asset losses. Asset security requires proactive protection—any negligence may lead to irreversible losses.
Digital Asset Security Operation Guide
Cold Wallet Selection and Initialization
When selecting and setting up a cold wallet, strictly follow the process to ensure asset security. The following steps can help you minimize risks:
- Purchase from official channels to avoid third-party sellers and prevent supply chain attacks.
- Check that the packaging is intact and has not been opened or tampered with.
- Initialize the device in a completely private environment, avoiding cameras and networked devices.
- Manually record the recovery phrase—never take photos or store it digitally.
- Verify the recovery phrase to ensure the backup is correct.
- Set a PIN or enable biometrics to enhance physical security.
- Install the official companion app, such as BiyaPay or other services that support cold wallet management, for convenient subsequent operations.
- Perform small-amount transfer tests to confirm the device and process are secure and reliable.
By following this process, you can effectively prevent common supply chain and initialization security risks.
Hardware Authentication Device Management
When managing hardware authentication devices, establish a multi-layered protection system. It is recommended to adopt the following measures:
- Implement a zero-trust security model—every access requires identity verification.
- Use hardware-based authentication methods to prevent software-layer bypasses.
- Conduct regular security audits to detect potential risks in a timely manner.
- Purchase devices directly from trusted suppliers and ensure packaging is undamaged.
- Check firmware version and configuration before use to prevent pre-installed malicious code.
- Utilize hardware security modules (HSM) to store keys and enhance security levels.
- Enable biometric recognition and remote wipe features to prevent asset theft if the device is lost.
- Strengthen physical controls to protect the device from environmental hazards.
- Develop business continuity plans to address physical threats or disasters.
Through these measures, you can significantly reduce the risk of unauthorized access or physical damage to hardware devices.
Emergency Response and Backup Plans
In digital asset management, you must establish comprehensive emergency response and backup mechanisms. It is recommended to:
- Collect key business-related information to enable rapid response during emergencies.
- Regularly assess risks and business impact and adjust backup strategies accordingly.
- Develop a comprehensive disaster recovery plan that incorporates cybersecurity best practices.
- Clearly define backup frequency to ensure data security and recoverability.
- Conduct regular emergency response drills to improve team collaboration and recovery efficiency.
- Integrate cybersecurity measures to defend against constantly evolving attack techniques.
- Perform simulation tests to verify the effectiveness of recovery plans.
Through scientific backup and emergency planning, you can maximize asset security and business continuity in the event of attacks, device damage, or natural disasters.
In digital asset management, you must always remember: never trust any code. Code vulnerabilities, automated attacks, and dependency risks persist. Only cold wallets and hardware authentication devices can effectively isolate private keys and prevent phishing and malware attacks. You can enhance asset security through the following measures:
- Cold wallets store private keys offline, isolating internet threats.
- Hardware authentication devices use encryption technology and secure storage to reduce risks from untrusted code in automated environments.
- Air-gapped storage solutions further protect sensitive credentials.
You should also implement comprehensive monitoring, deploy automated threat detection, conduct regular security audits, and continuously follow digital asset security developments. Continuous learning and improving security awareness enable you to proactively defend against emerging threats and truly put security first.
FAQ
What is the difference between a cold wallet and a hardware wallet?
You can understand a cold wallet as a method of offline private key storage, while a hardware wallet is a dedicated device with physical isolation and secure chips that can prevent malware attacks.
Why can’t code auditing completely eliminate risks?
You will find that code auditing can only detect some vulnerabilities—both automated tools and manual review may miss complex logic or hidden backdoors. Asset security still requires multi-layered protection.
How to choose a secure wallet device?
You should prioritize purchasing hardware wallets from official channels, check packaging integrity, and avoid third-party supply chain risks. It is recommended to regularly update firmware to ensure device security.
Which scenarios are hot wallets suitable for?
You can use hot wallets for daily small payments and fast transactions. Hot wallets are convenient but carry higher risk—not recommended for long-term storage of large amounts of assets.
How to handle asset loss in an emergency?
You should immediately freeze related accounts, contact platform customer service, and check backups and recovery phrases. It is recommended to prepare an emergency plan in advance to improve asset recovery efficiency.
*This article is provided for general information purposes and does not constitute legal, tax or other professional advice from BiyaPay or its subsidiaries and its affiliates, and it is not intended as a substitute for obtaining advice from a financial advisor or any other professional.
We make no representations, warranties or warranties, express or implied, as to the accuracy, completeness or timeliness of the contents of this publication.
Related Blogs of

How to Pay for Claude Max: Subscription Requirements, Renewal Methods, and Common Questions

How to Choose a Virtual Card for AI Service Subscriptions: Payment Scenarios for ChatGPT, Claude, and More
Choose Country or Region to Read Local Blog
Contact Us
BIYA GLOBAL LLC is registered with the Financial Crimes Enforcement Network (FinCEN), an agency under the U.S. Department of the Treasury, as a Money Services Business (MSB), with registration number 31000218637349, and regulated by the Financial Crimes Enforcement Network (FinCEN).
BIYA GLOBAL LIMITED is a registered Financial Service Provider (FSP) in New Zealand, with registration number FSP1007221, and is also a registered member of the Financial Services Complaints Limited (FSCL), an independent dispute resolution scheme in New Zealand.



















