Protecting Your Wealth Bottom Line: Privacy Protection Strategies for High-Net-Worth Individuals in Global Multi-Jurisdiction Asset Allocation
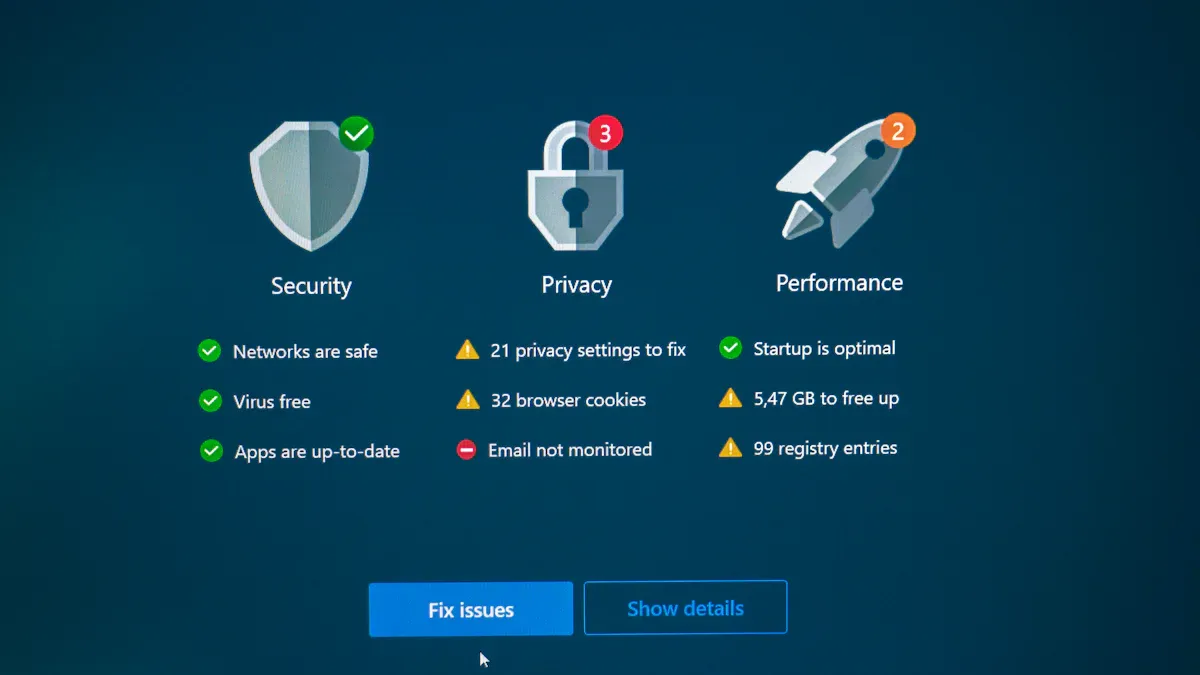
Image Source: unsplash
When you allocate assets globally, you often face real challenges such as identity information exposure and data breaches. Protecting personal privacy is not only about asset security but also directly concerns the bottom line of your wealth. You need to rely on compliant structures, implement information isolation, adopt technical encryption, and collaborate with professional teams to effectively safeguard your personal assets and long-term family wealth stability.
Core Key Points
- Protecting personal privacy is the key to ensuring wealth security. Use compliant structures and information isolation to reduce the risk of identity exposure.
- Regularly review information disclosure processes to ensure compliance with local laws and regulations and avoid excessive exposure of personal data.
- Adopt layered isolation strategies to store sensitive information, strengthen control over assets and data, and reduce data breach risks.
- Build a professional team combining legal, financial, and technical experts to dynamically respond to global regulatory changes and optimize privacy protection solutions.
- Choose financial platforms with high-standard privacy protection measures to ensure the security and compliance of cross-border asset allocation.
Privacy Risks in Global Asset Allocation

Image Source: pexels
Information Leakage and Identity Exposure
When you allocate assets globally, personally identifiable information (PII) and KYC data are highly vulnerable to leakage. Once sensitive data such as name, date of birth, and social security number are stolen, the risk of identity theft increases significantly. Financial accounts and transaction records—including bank accounts, brokerage accounts, and investment history—are also frequently exposed due to platform vulnerabilities or operational errors, leading to direct financial losses. Investment plans, financial goals, and risk tolerance questionnaires, if obtained by third parties, can undermine your privacy foundation and trust.
- Main sources of leakage include:
- Personally identifiable information and KYC data
- Financial accounts and transaction records
- Investment plans and personal financial goals
Tax Compliance and Data Sharing
International tax compliance regulations (such as FATCA and CRS) require financial institutions to collect and report taxpayer information across borders. You face data-sharing risks; increased transparency brings hidden dangers of data breaches and unauthorized access. In the context of automatic information exchange, protecting privacy becomes more complex. Public disclosure of data can not only cause embarrassment but also create security risks. In recent years, tax authorities have frequently suffered cyberattacks and data breaches, further intensifying information security concerns.
When allocating assets across multiple jurisdictions, you must pay attention to the dual challenges of tax compliance and data security.
Financial Institutions and Platform Security
Global financial institutions and platforms have various security vulnerabilities. Risks such as identity theft, wire fraud, credit card fraud, and real estate transaction fraud occur frequently. Security incidents on financial platforms can expose your sensitive personal and financial information, increasing the possibility of targeted attacks and emotional blackmail. Platform leaks are often accompanied by delayed notifications, with data flowing freely and serious consequences. Medical information leaks are particularly dangerous, as the intersection of personal medical and financial capabilities can easily lead to insurance discrimination and harassment. The Genea IVF data breach incident exposed 700GB of highly sensitive medical files, highlighting the urgency of privacy protection in global asset allocation.
Wealth Bottom Line and Privacy Protection Principles
Compliance and Data Minimization
When allocating assets globally, you must always adhere to the principle of compliance. The wealth bottom line is not only reflected in asset security but also in legality and compliance. You need to reasonably disclose only necessary information according to regulations in different regions and avoid excessive exposure of personal data. The data minimization principle requires you to provide only the most essential data to financial institutions, trust structures, or family offices. This can reduce the risks of identity exposure and data breaches.
Compliance is the core safeguard of your wealth bottom line. You should proactively understand local privacy laws, regularly review information disclosure processes, and ensure every asset allocation meets local legal requirements.
You also need to pay attention to multi-dimensional measures including physical security, technology integration, personnel & procedures, and family digital protection:
- Physical security: multi-layer protection, including buildings and safe rooms
- Technology integration: use technology for early warning and response
- Personnel and procedures: customized protection processes and risk assessments
- Family digital protection: guard against cybercrime and protect family members’ privacy
Layered Isolation and Dynamic Adjustment
You can further protect your wealth bottom line through layered isolation strategies. Storing sensitive information such as financial records and identity data in layers can significantly reduce data breach and intrusion risks. Data isolation not only improves legal compliance but also enhances your control over assets and information.
- Enhanced protection: isolate data to lower the probability of sensitive information leakage
- Improved legal compliance: help meet various data security protocols and reduce penalty risks
- Increased control: define access permissions to ensure only authorized personnel can access specific information
You should also dynamically adjust isolation strategies according to changes in global asset allocation. Regularly assess risks and promptly optimize isolation layers and access permissions. This ensures your privacy protection solution always aligns with the wealth bottom line and adapts to changes in the global regulatory environment.
Privacy Protection Solutions and Practical Implementation

Image Source: pexels
Offshore Trusts and Family Offices
You can build multi-layered privacy protection barriers by establishing offshore trusts and family offices. Offshore trusts offer unique privacy advantages in different jurisdictions. For example, Nevis, Cook Islands, and Liechtenstein provide strong legal and information protection for high-net-worth individuals. The table below shows key features of major jurisdictions:
| Jurisdiction | Key Features | Target Users |
|---|---|---|
| Nevis | Offers anonymous LLCs and trusts with strong creditor protection and resistance to legal challenges | High-net-worth individuals |
| Cook Islands | Law prioritizes the interests of the settlor and can resist foreign court orders | Ultra-high-net-worth individuals |
| Liechtenstein | Combines civil law confidentiality with legal personality; allows wealth to be managed as an independent entity without public disclosure | High-net-worth individuals and wealth managers |
When establishing a family office, you need to focus on cybersecurity, data protection, and confidentiality. Family offices are often targets for data breaches and cyberattacks due to the lack of formal protection systems. You should ensure all third-party service providers adopt the highest level of protection measures and continuously update compliance strategies according to changes in technology and legal environments. Modern luxury assets (such as superyachts and private jets) also increase the complexity of privacy protection. You need to develop customized protection plans covering physical security, technology integration, personnel management, and family-wide digital protection to prevent cybercrime and information leaks.
Hong Kong and Global Financial Platforms
When selecting Hong Kong and global financial platforms, prioritize data security and privacy protection measures. Hong Kong licensed banks maintain high standards in compliance and data protection. According to Article 30 of the Basic Law, Hong Kong protects freedom of communication and privacy, but police have the right to conduct electronic surveillance in national security-related cases. When allocating assets cross-border, you need to pay attention to the transfer and storage of personal data and ensure all operations comply with Section 33 of the Personal Data (Privacy) Ordinance.
At the execution level, a platform’s value is not only whether it can move funds, but whether identity checks, access control, and sensitive data transmission are handled in separate layers. A product such as BiyaPay, positioned as a multi-asset trading wallet, fits more naturally into a broader privacy-protection framework covering payments, investing, trading, and fund management.
If your allocation involves cross-border fund movement or multi-currency conversion, it is generally safer to use clear, traceable entry points, such as the remittance service for transfers or the exchange-rate comparison tool to verify costs first. For high-net-worth individuals, that kind of structured workflow can help reduce privacy risks created by verbal instructions, ad hoc coordination, or unnecessary data exposure.
Global financial platforms are continuously strengthening privacy protection. You will find that more and more platforms adopt stricter regulations and compliance requirements, use artificial intelligence to improve data privacy management efficiency, and pay attention to the security of decentralized technologies such as blockchain. BiyaPay as a global payment and cryptocurrency exchange platform supports USDT ↔ USD/HKD conversion and US/Hong Kong stock fund flows, providing privacy protection for multi-currency asset allocation and cross-border capital movement. When using BiyaPay, you can reduce the risk of sensitive information leakage through the platform’s multi-factor authentication and encryption measures, safeguarding your wealth bottom line.
Technical Encryption and Cybersecurity
In the process of global asset allocation, you must adopt advanced encryption technologies to protect sensitive data. The table below summarizes mainstream encryption technologies and their features:
| Encryption Technology | Description |
|---|---|
| Advanced Encryption Standard (AES) | Widely used symmetric encryption algorithm supporting different key lengths with high security |
| RSA Encryption | Asymmetric encryption algorithm suitable for protecting sensitive information with multiple key length options |
| Quantum Key Distribution (QKD) | Uses quantum mechanics to create secure keys and can detect tampering attempts |
You can combine encryption transmission and multi-factor authentication from platforms like BiyaPay to enhance the security of cross-border payments and asset transfers. High-net-worth individuals are often targets of cybercriminals. You should conduct regular proactive risk assessments and real-time monitoring to prevent cyberattacks and financial fraud. Cross-border transactions involve multiple legal jurisdictions with complex compliance; cybersecurity measures must cover the entire process of data transmission, storage, and access to truly protect your wealth bottom line.
Information Isolation and Authorization Management
In international wealth management, you should adopt layered isolation and fine-grained authorization management. Best practices include:
- Implement data isolation through ACID transactions to ensure reliability and consistency of database operations.
- Regularly back up and restore data, keeping redundant copies to improve data security.
- Select database management systems that support ACID properties (such as SQL platforms, Oracle, Microsoft SQL Server, PostgreSQL, MySQL).
- Extensively test applications to ensure normal operation under various failure scenarios.
You should set access permissions for different levels of sensitive information, ensuring only authorized personnel can access specific data. Platforms like BiyaPay support multi-level permission management to help you achieve layered isolation of assets and information, reducing data breach risks.
Professional Team Collaboration
You need to assemble a professional team of legal, financial, and technical experts to jointly safeguard personal privacy. Legal experts help you build asset protection strategies to ensure wealth security. Financial experts assist in tax-efficient structural design and wealth management. Technical experts focus on cybersecurity to protect personal information and assets from cyber threats. You should remain cautious in all online interactions, verify all personal information requests, create unique passwords for each account, and use multi-factor authentication.
| Role | Description |
|---|---|
| Legal Expert | Helps build asset protection strategies to ensure wealth security for high-net-worth individuals |
| Financial Expert | Assists in tax-efficient structuring and financial planning to optimize wealth management |
| Technical Expert | Focuses on cybersecurity measures to protect personal information and assets from cyber threats |
Through collaboration with a professional team, you can dynamically respond to global regulatory changes, continuously optimize privacy protection solutions, and truly achieve long-term safeguarding of your wealth bottom line.
Key Compliance Points in Major Regions
Europe and US Privacy Regulations
When allocating assets in Europe and the US, you must strictly comply with multiple privacy protection regulations. Europe’s General Data Protection Regulation (GDPR) imposes extremely high requirements on personal data processing. You need to ensure all data processing activities have a lawful basis, such as explicit consent, contractual necessity, or legal obligation. GDPR also requires implementation of technical and organizational measures to ensure data security, including regular Data Protection Impact Assessments (DPIA) and maintaining detailed records of processing activities. In the United States, the Foreign Account Tax Compliance Act (FATCA) emphasizes cross-border asset transparency, requiring financial institutions to report relevant account information. The Common Reporting Standard (CRS) developed by the OECD also requires you to cooperate with automatic information exchange to enhance global asset transparency.
- Key compliance points in Europe and the US include:
- Clearly establish lawful basis for data processing and obtain necessary consent
- Maintain records of processing activities and regularly assess risks
- Implement strong cybersecurity measures to prevent data breaches
- Collaborate with trusted advisors to dynamically respond to regulatory changes
Global financial platforms such as BiyaPay provide multi-factor authentication and encryption measures for Chinese-speaking users, helping you achieve a balance between asset allocation and privacy protection under compliance requirements.
Asia and Offshore Jurisdiction Requirements
When allocating assets in Asia and offshore jurisdictions, you face diverse privacy regulations. Some countries (such as South Korea and Vietnam) have strict data localization requirements, mandating that personal data be stored within their borders. Before conducting cross-border data transfers, you must inform the relevant individuals in advance and obtain explicit consent. Under the principle of sovereignty, data remains subject to the laws of the collecting country regardless of where it is actually stored. You also need to ensure all partners and service providers comply with cross-border privacy rules, and contracts should include mandatory audit and data transfer clauses.
- Recommended measures for compliance in Asia and offshore jurisdictions:
- Map and classify all international data flows, identifying sources, destinations, and partners
- Conduct data transfer and risk assessments to ensure every cross-border operation is traceable
- Choose compliant financial platforms such as BiyaPay, utilizing its multi-level permission management and encryption technology to reduce data breach risks
By dynamically adjusting compliance strategies, you can continuously protect personal privacy and global asset security in the ever-changing Asian and offshore regulatory environments.
Protecting Your Wealth Bottom Line: Common Pitfalls and Risks
Over-Reliance on Single Methods
When allocating assets globally, you may mistakenly believe that a single privacy protection method is sufficient to address complex risks. For example, some high-net-worth individuals rely solely on offshore trusts or a single financial platform, neglecting the synergistic effect of multi-layered structures and technical measures. Single-method approaches easily create security weaknesses and cannot cover multi-dimensional threats such as identity, data, network, and compliance. If you only focus on legal structures, you may overlook technical risks of cyberattacks and data breaches. If you only rely on technical encryption, you may face legal penalties due to compliance oversights.
You need to build a multi-dimensional, dynamic privacy protection system that organically integrates legal structures, technical encryption, information isolation, and professional team collaboration to truly protect your wealth bottom line.
Neglecting Compliance and Technology
If you neglect compliance and technology in your privacy protection plan, serious consequences can easily arise. Globally, governments and regulators continue to strengthen laws and regulations to protect consumer rights. Future compliance requirements will become even stricter, and non-compliance will face high fines and penalties. Neglecting compliance and technology not only exposes you to legal, financial, and reputational risks but may also undermine the effectiveness of privacy regulations, leading to data breaches and exploitation of personal information.
- Main risks of neglecting compliance and technology include:
- Facing high fines and legal proceedings
- Exposure of assets and personal information
- Damage to personal and family reputation
- Difficulty gaining trust from partner institutions and family members
You should recognize that compliance is not just about avoiding penalties—it is key to building trust and enhancing global competitiveness. Effective risk management maximizes the value of personal data while minimizing potential negative impacts. Only by continuously paying attention to compliance and technological developments can you achieve long-term wealth security in global asset allocation.
To protect your wealth bottom line, you must adopt multi-dimensional, dynamic, and compliant privacy protection strategies. You can combine legal structures, technical measures, professional teams, and global compliance requirements to truly achieve wealth security.
- Continuously monitor privacy protection trends, regularly review processes, and adapt to legal and family changes so your asset protection strategy remains effective.
You should stay informed about industry developments and proactively optimize solutions to ensure every step meets global regulatory requirements.
FAQ
After establishing an offshore trust, how do you ensure information is not leaked?
You should choose jurisdictions with strict confidentiality regimes and regularly review trust documents. You also need to collaborate with a professional legal team to ensure all information disclosures comply with legal requirements.
When using Hong Kong and global financial platforms, how do you assess their privacy protection level?
You can review the platform’s privacy policy and focus on data encryption, access controls, and compliance certifications. You should also prioritize regulated Hong Kong licensed banks or internationally reputable financial service providers.
How do you balance compliance and privacy in global asset allocation?
You need to reasonably disclose information according to local regulations and adopt the data minimization principle. You should also combine legal structures with technical measures and dynamically adjust privacy protection strategies to achieve both compliance and privacy.
How do you prevent data breach risks during cross-border fund flows?
You should use platforms with end-to-end encryption and multi-factor authentication. You also need to regularly update access permissions, monitor account activity, and promptly detect abnormal operations.
How do you build a professional team to enhance privacy protection
*This article is provided for general information purposes and does not constitute legal, tax or other professional advice from BiyaPay or its subsidiaries and its affiliates, and it is not intended as a substitute for obtaining advice from a financial advisor or any other professional.
We make no representations, warranties or warranties, express or implied, as to the accuracy, completeness or timeliness of the contents of this publication.
Related Blogs of

What to Do When OpenAI API Top-Up Fails? Balance, Prepaid Billing, Charges, and Credit Arrival Checks

Claude Pro and Claude API Payment Guide: Cards, Billing and Failed Payment Fixes
Choose Country or Region to Read Local Blog
Contact Us
BIYA GLOBAL LLC is registered with the Financial Crimes Enforcement Network (FinCEN), an agency under the U.S. Department of the Treasury, as a Money Services Business (MSB), with registration number 31000218637349, and regulated by the Financial Crimes Enforcement Network (FinCEN).
BIYA GLOBAL LIMITED is a registered Financial Service Provider (FSP) in New Zealand, with registration number FSP1007221, and is also a registered member of the Financial Services Complaints Limited (FSCL), an independent dispute resolution scheme in New Zealand.



















